Interests

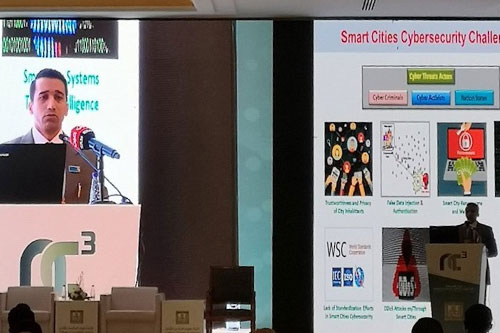
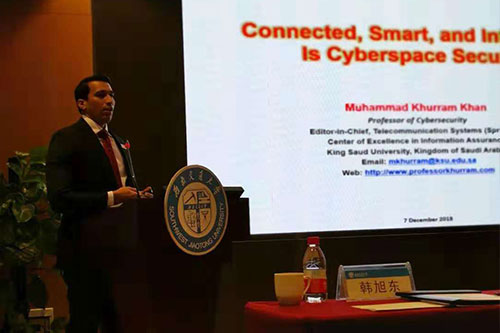
Cyber Security
Awareness and Education Cybersecurity Ecosystem

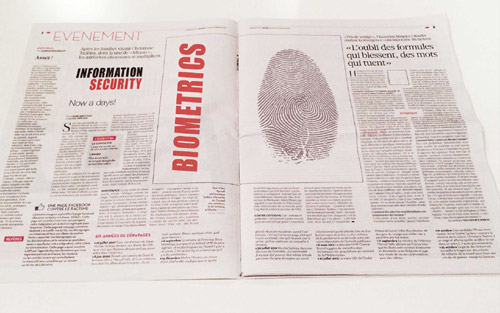
Digital Authentication
Identity Management Authentication Protocols Internet of Things

Biometrics
Personal Identification Authentication Protocols Biometrics System Security

Cloud Computing Security
Cloud Authentication
Cloud Data Security
Cloud Privacy

Multimedia Security
Multimedia Forensics
Digital Quran Security
Digital Contents Security

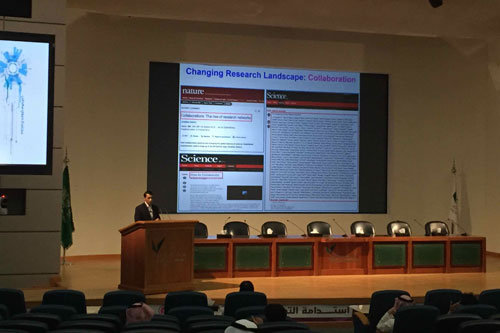
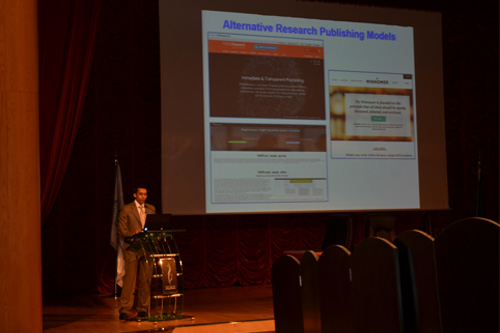
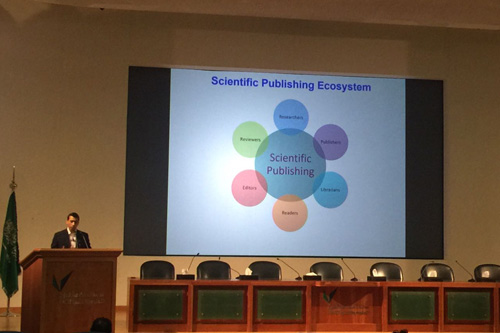
Technological Innovation Management
Open Innovation in GCC
Innovation Ecosystem